Kameron Kennemer: Welcome back to another exciting episode of The ITcurio Podcast. Your source for technology insights and strategies. I’m Kameron Kennemer, a tech enthusiast with a background in sales and marketing, as well as IT. Today, we have a captivating episode in store where we’ll be exploring the world of cybersecurity and cloud computing, specifically tailored for small to medium-sized businesses. And I am joined, of course, by the IT wizard himself.
Kameron Kennemer: With over 30 years of experience, GE Forman, get ready to level up your tech game, folks. But let’s dive in and let’s get started. D.J., how are you today?
DJ Forman: I’m doing pretty good, Kameron. Thank you for asking. How about you?
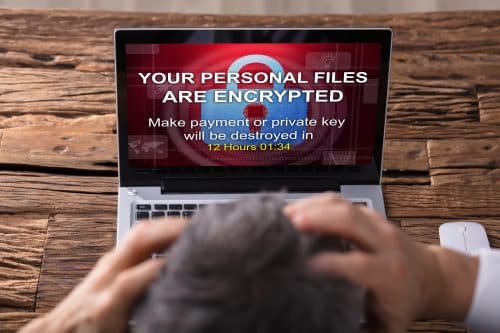
Kameron Kennemer: I’m doing pretty good too. I’m excited to talk about IT cybersecurity and maybe help some businesses out there figure some things out. What do you think about that? Helping people is always rewarding. In today’s increasingly interconnected world, cybersecurity is obviously a top concern for businesses. They want to safeguard sensitive data and protect against cyber threats. This applies not only to larger businesses but also to small and medium-sized ones.
Kameron Kennemer: However, small and medium-sized businesses face unique challenges in maintaining a strong cybersecurity posture, as they may not have as many resources as larger companies. As our resident cybersecurity guru, D.J., I’d love to hear your insights on how businesses can establish a cybersecurity strategy. What are the best practices for defending against these new threats? How can business owners effectively manage and ensure the safety of their customers’ data, digital assets, and overall security?
DJ Forman: Let’s take it one question at a time. It’s important to acknowledge that there is no foolproof way to achieve 100% security or prevent all possible attacks. However, there are measures businesses can take to protect themselves. One approach is to deploy multiple layers of security and employ experts who can analyze incoming data and identify potential threats. This involves tasks such as threat hunting, penetration testing, and other proactive measures. Nevertheless, these steps can become expensive and time-consuming, prompting a need to weigh the cost-benefit ratio and consider security compliance concerns.
DJ Forman: Speaking of compliance, it’s crucial to consider various regulatory frameworks depending on the industry. For instance, many are familiar with HIPAA for healthcare, but there are also regulations for credit cards, the Department of Defense, and others. Even if a business is not legally required to comply with specific rules or laws, privacy laws should be considered as a baseline standard.
Read the full article here……………