……….Continued
DJ Forman: So, where should businesses start? It’s advisable to target the low-hanging fruit first, the most significant vulnerabilities. We strongly recommend three essential measures. First, endpoint protection, which encompasses more than traditional antivirus technology. It involves comprehensive network monitoring, not just file-based detection. Second, implementing multi-factor authentication (MFA) or two-factor authentication (2FA) adds an extra layer of security with something you have (e.g., a physical token or a mobile app) and something you know (e.g., a password). Finally, advanced email protection is crucial as phishing emails remain the number one attack vector.
DJ Forman: By prioritizing these measures, businesses can enhance their cybersecurity defenses and mitigate risks effectively.
DJ Forman: So those are the three big ones that you really should consider to be the bare minimum. That’s what you’ve got to do. Now there are layers beyond that, and those layers aren’t just a cost line item in terms of monthly software licensing costs, but also the care and feeding—the care and feeding that is required.
DJ Forman: Right. So you have these tools in place. Let’s say you have penetration testing in place. What that’s going to do is scan the outside and inside of the network and identify things that may need patching. It could be a hole in a firewall or a device that’s improperly configured and wide open to the world.
DJ Forman: There are two types of penetration testing. The first is penetration test scanning, which is what most people really need. It does exactly what I described. Then there’s human penetration testing, where an actual person tries to take advantage of any vulnerabilities. However, that comes at a significant cost. Sorry, go ahead.
Kameron Kennemer: I was just going to say, you know, one of the things maybe I wonder if that deters people from taking these precautions myself. I remember times when I got quite frustrated with all the different passwords that I had to have and the constantly changing passwords. And I remember thinking man, is it really necessary to create all of this trouble?
Kameron Kennemer: I mean, that was before I got into all of this and, you know, really saw how important it is. But I think there might be a perspective out there where business owners and managers might not want to deal with this because they just see it as a hassle and they don’t understand how important it is.
Kameron Kennemer: But there are some new things that have come down the pipeline like you’re talking about the password, the multifactor authentication, and some of the apps that you can get on your phone to help you with that. And they have completely passwordless ways to go now that are a lot simpler than it used to be. Isn’t that true?
DJ Forman: It’s absolutely true. There are many different ways people can gain unauthorized access. You can implement all these security measures, but if there’s a vulnerability that bypasses all of them, then what’s the point, really? Even with multiple layers of security, what happens when someone using the computer still clicks on something they shouldn’t have?
DJ Forman: And what if what they clicked on isn’t caught by the tools in place? That’s called a zero-day vulnerability, something that hasn’t been identified or categorized yet. It can be disheartening, but that’s why we advocate for a reasonable and realistic approach and understand the need to embrace a certain level of ambiguity. You won’t always have all the answers.
DJ Forman: People have this misconception that servers can provide a complete record of everyone’s actions at any given moment. However, servers don’t do that by default. You need to set that up and often use special software. It’s challenging to determine where that line is, which is why you should engage with a professional group that can help you make informed decisions.
DJ Forman: Find experts who have experience and have been through similar situations. It doesn’t mean that they’re always right. That’s why professional organizations recommend using a third party to double-check your security once a year. It may be a bitter truth and hard to accept, but that’s the reality of the internet. It’s still a bit like the Wild West out there.
Kameron Kennemer: E.J., I’d like to shift our focus to the cloud a little bit now and how that relates to security, maybe ways that might be helpful to businesses and the pluses and minuses of it versus having your equipment on-site in a more traditional manner. The cloud offers businesses a flexible and scalable infrastructure, enabling them to streamline their operations and enhance efficiencies.
Kameron Kennemer: It’s becoming more integrated into the modern business landscape. Can you talk a little bit about that? I know you’re well-versed in cloud computing. Can you share with us how small to medium-sized businesses can use these cloud solutions and discuss the considerations they should keep in mind? How can cloud technologies improve operations or save money, if possible? What choices should business owners make?
DJ Forman: We frequently have conversations about this, almost on a daily basis, definitely on a weekly basis. Many people have the idea of moving all their stuff to the cloud, assuming it will be inherently more secure and less expensive. However, the reality is different. When you shift to the cloud, you’re transitioning from capital expenditure (CapEx) to operational expenditure (OpEx).
DJ Forman: This is the value proposition of most Software-as-a-Service (SaaS) solutions like QuickBooks Online, Microsoft 365, and Gmail. It’s essential to know that the cloud is not automatically more secure or cost-effective. You end up paying monthly costs for similar levels of protection.
DJ Forman: One fallacy is the belief that the cloud is much more secure. While it has certain advantages, it’s not as robust as people think. For example, if you want to host your website on Amazon Web Services, it comes with basic security and firewall protection. But if you need a web application firewall for a shopping website or one with dynamic content and scripting, that’s an additional cost.
DJ Forman: Bandwidth consumption is another consideration. It’s challenging to predict the amount of traffic a site will receive. Web developers and hosting solutions like Azure and Amazon offer tools for analysis, but it’s important to keep in mind that they are the ones providing the tools.
DJ Forman: I’m not implying dishonesty, but you should not assume everything. Talk to your provider or reach out to us. We’re happy to discuss these topics and build relationships, even if you have another provider.
Kameron Kennemer: Perfect. Another topic that keeps popping up every time I browse online is something called Zero Trust Network Access (ZTNA), and many businesses may be wondering what it is and if they should implement it. Could you explain what ZTNA is, its benefits, and whether it’s important for business owners to consider?
DJ Forman: So zero trust or ZTNA, Zero Trust Network Architecture, is all great stuff. It’s not actually new, but the terminology is new and definitely more appealing. Instead of saying “closed, closed,” we now say zero trust, which captures people’s attention. The basic idea is to have everything closed except for the necessary open doors.
DJ Forman: Zero trust is granular down to the level of individual users. Each person has access to specific doors that are not accessible to others, like front desk staff. The concept is that even if a bad actor gains access to the network, they wouldn’t be able to see anything unless they have elevated credentials. This approach protects sensitive data, even in scenarios where a contractor with malicious intent infiltrates an office.
DJ Forman: Most people are professional and trustworthy, but it’s important to acknowledge that bad actors do exist. Zero trust architecture provides the best way to protect yourself. However, the question is whether it’s the most cost-effective option. Implementing zero trust involves not just deploying software or paying for it, but also considering management time, staff time, and the labor overhead it creates.
DJ Forman: For example, with a Data Loss Prevention (DLP) solution deployed, it identifies and classifies data, such as who accessed it, when, and where. However, determining the importance or classification of the data requires user input, and IT personnel may not necessarily know the significance of every file. While some situations, like a file containing Social Security numbers, are obvious, many others are not straightforward.
Kameron Kennemer: One of the benefits of working with another company to handle IT management is having a team of people to help. Could you talk a bit about that?
DJ Forman: Absolutely. When it comes to IT, the question is, can you do it and how? For most small to medium-sized businesses, the answer is no. They may not have the budget or may have hired someone who handles IT on the side. We understand that cost is a factor, and that’s why we offer secure systems and support without requiring an enterprise-class budget.
DJ Forman: At the end of the day, a computer is just a tool to get your job done, like a hammer or a vehicle. You don’t want to spend all day working on the tool itself. That’s where companies like ours come in. We provide a full-blown managed IT department, offering on-site support as needed and 24/7 assistance. Businesses can benefit from enterprise-class service without the hefty price tag.
DJ Forman: Absolutely, Kameron. Business continuity and disaster recovery (BCDR) are crucial components in responding to a data breach or attack. When all preventive measures fail and a breach occurs, the focus shifts to minimizing the impact and recovering operations as quickly as possible.
DJ Forman: A reliable BCDR solution, such as the one offered by Datto, can be instrumental in this process. The solution involves having a device on-premises that serves as a robust server, capable of running the necessary applications and systems. Regular image backups are taken, capturing the entire server’s state, including software and data.
DJ Forman: With these backups in place, in the event of a breach or disaster, the server can be quickly restored from the most recent backup. This means that within a matter of minutes or hours, depending on the scale of the infrastructure, the business can be up and running again, minimizing downtime and ensuring continuity of operations.
DJ Forman: Additionally, cloud replication plays a vital role in BCDR. The backups are securely replicated to the cloud, providing an off-site backup that can be accessed in the event of a complete building failure or catastrophic event. By running servers from the cloud, businesses can resume operations while they address the physical damage or infrastructure issues.
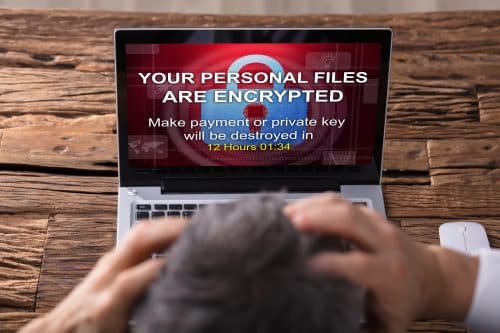
DJ Forman: It’s important to note that BCDR is not just about recovering from a breach or disaster, but also addressing the aftermath. It allows businesses to rollback to a clean state before the attack occurred, mitigating the impact of ransomware or other cybersecurity attacks.
DJ Forman: Ultimately, having a solid BCDR solution in place ensures that businesses can swiftly recover, protect their data, and maintain business continuity in the face of unexpected events. It’s a proactive approach that helps businesses minimize the impact of breaches and quickly get back on track.
Kameron Kennemer: Thank you for providing that detailed explanation, DJ. It’s reassuring to know that businesses can rely on a robust BCDR solution to mitigate the effects of a breach or disaster. Having a plan in place and partnering with professionals who can implement and manage these solutions is crucial for businesses of all sizes.
Kameron Kennemer: Businesses also have other responsibilities when it comes to reporting data breaches, correct?
DJ Forman
You’re correct. In the event of a data breach or security incident, businesses have obligations to their customers and individuals whose information may have been compromised. These obligations may include client communication, which can be legally required depending on the nature of the incident.
DJ Forman
There are costs associated with such communication, especially when privacy laws come into play. For example, some states have notification laws that require businesses to inform individuals if their personal information has been compromised. This communication often needs to be done through registered mail, which can be time-consuming and expensive.
DJ Forman
Furthermore, businesses may need to reach out to their cybersecurity insurance provider, report the incident to law enforcement agencies such as the FBI and local authorities, and potentially involve legal and forensic teams provided by their insurance underwriters. The costs and procedures involved in these steps can vary depending on the specific insurance policy and the nature of the incident.
DJ Forman
The landscape of obtaining cybersecurity insurance has also changed. Previously, it was easy to get coverage without much due diligence. However, after significant settlements were paid out, insurance companies have become more cautious and now require businesses to meet certain security requirements. This includes having security solutions in place, written policies, incident response plans, and regular training.
DJ Forman
To address the importance of cybersecurity awareness, we offer free cybersecurity training for businesses. In these classes, I try to make the training engaging and relevant. I avoid using outdated or boring information. Instead, I make it modernized and relatable. Sometimes, I use provocative statements to grab attention and encourage individuals to take personal responsibility for cybersecurity.
DJ Forman
The goal is to make the training interactive and enjoyable by incorporating real-life examples, case studies, and interactive activities. By doing so, participants can better understand the relevance of cybersecurity and are more likely to apply the knowledge in their daily work and personal lives.
DJ Forman
Absolutely, it’s a team effort, and everyone plays a role in cybersecurity. The reality is that individuals who are not computer experts may not understand all the technical aspects of cybersecurity. They send emails without knowing the intricacies behind them. But that’s okay because their expertise lies in their own job, and they don’t need to be cybersecurity experts.
DJ Forman
To make cybersecurity training more interesting and engaging, we try to modernize and relate it to everyday situations. We avoid using outdated or boring information. We may even incorporate elements of magic or shock to grab attention and keep participants engaged. The goal is to make the training enjoyable and relevant, so people don’t fall asleep or lose interest.
DJ Forman
When structuring the classes, we focus on what individuals can actually control and take action on. This often centers around email and web browsing, as these are common areas of vulnerability. We teach participants to recognize red flags, be aware of what should make them uncomfortable or nervous, and understand what is normal behavior. By focusing on practical aspects, such as identifying phishing emails or suspicious URLs, individuals can make better decisions to protect themselves and their organization.
DJ Forman
We believe that interactive training is more effective than simply watching videos or filling out questionnaires. While videos have their place, they should be used in conjunction with other training methods, such as in-person sessions, phishing testing, and ongoing reinforcement throughout the year. This can include company newsletters, immediate feedback on phishing tests, and continuous education to reinforce good cybersecurity practices.
DJ Forman
The goal is to ensure that individuals retain the knowledge and apply it in their daily work and personal lives. By providing engaging and relevant training, we can empower individuals to be more aware of cybersecurity risks and make informed decisions to protect themselves and their organizations.
Kameron Kennemer:
That’s a great approach, D.J. It’s important to make cybersecurity training engaging and relatable so that people can retain the knowledge and apply it in their daily lives. By focusing on practical aspects and using interactive methods, such as in-person sessions and phishing tests, individuals are more likely to understand the importance of cybersecurity and take appropriate actions to protect themselves and their organization.
DJ Forman:
Absolutely. It’s not enough to simply watch videos or fill out questionnaires. People often don’t pay full attention to those and may not retain the information. By incorporating interactive elements, such as immediate feedback on phishing tests, individuals can see firsthand the red flags they missed and learn from their mistakes.
Kameron Kennemer:
I completely agree. It’s about creating a learning experience that is effective and memorable. Ongoing reinforcement is also crucial. Cybersecurity should be a continuous effort, not a one-time training session. By providing regular reminders and updates, such as through newsletters or additional training modules, individuals can stay informed and vigilant against emerging threats.
DJ Forman:
Exactly. Cybersecurity is an evolving landscape, and new threats emerge all the time. By keeping individuals informed and engaged, they can adapt to changing circumstances and make better decisions to protect themselves and their organization. It’s important to foster a
culture of cybersecurity awareness where everyone understands their role and takes responsibility for maintaining a secure environment.
Kameron Kennemer:
Absolutely. Cybersecurity is a collective effort, and it’s important for organizations to invest in training and awareness programs that empower their employees. By doing so, they can strengthen their overall security posture and reduce the risk of cyber incidents. Thank you, D.J., for sharing your insights and emphasizing the importance of engaging cybersecurity training.
DJ Forman:
You’re welcome, Kameron. It was my pleasure to discuss this important topic. Cybersecurity training is not only necessary but can also be engaging and enjoyable when approached with the right methods. By educating individuals and fostering a culture of security awareness, we can create a safer digital environment for everyone.
DJ Forman: They’re very similar looking, but not that happens all the time. And so, you know, through things like that, people go, “Oh, right, right.” Kameron Kennemer: It’s for a gig.
DJ Forman: It’s easy for me to be talking about that kind of stuff. We understand there’s a major difference between an “L” and a “1” and an “I” visually on the screen. There might not be much difference. They’re absolutely different in terms of what the computer looks at and sees. Not everybody gets that, unfortunately, but nor should they, frankly. That’s the big thing here. We work with a lot of doctors, a lot of lawyers, very educated, very smart people.
DJ Forman: They don’t really know much about their computers. I mean, I’m a human. I have a body. I go to the doctor. But does that mean I should know everything that the doctor’s doing when they take my blood test and they send it off? It’s magic. I don’t know how that works. With cybersecurity, it has been much the same.
DJ Forman: It’s kind of like it’s magic. I don’t know how it works, but we’ve gotten to the point now where we need to be more aware. They’re similar in healthcare these days, to be honest.
You really have to be your own advocate. And I’m going to say it’s the same with cybersecurity. We really need to be here.
Kameron Kennemer: Absolutely. I think that’s a wrap. That concludes another information-packed episode of the IT Curio podcast. We hope you gained some valuable insights and actionable tips for your business. Remember, staying ahead in the digital era requires continuous learning and change. Be sure to visit our website at Curio Icon, where you can register for our free live cybersecurity awareness training program hosted by the amazing D.J. Forman to protect your business.
Kameron Kennemer: Thanks for tuning in to the show, and until next time, stay curious and embrace technology. Thank you very much.

Pingback: Cybersecurity Awareness - Episode 3 - Protecting Your Business