
DJ Forman [00:00:43] Not for me. With me!
Kameron Kennemer [00:00:45] I’m working with you. That’s absolutely right. And it’s been really great experience so far. I wanted to thank you for the opportunity to help you make this podcast and to help you build it. I think that we’ve got a great team and I really look forward to getting out there and helping businesses. I was hoping that you could tell our listeners a little bit about you, a little bit about ITque, and what your vision is for the company. You know, just anything else that you’d like to talk about.
DJ Forman [00:01:12] Oh, is that all? No problem. We are a boutique quality enterprise class I.T provider where it’s called an MSSP managed services provider. It’s one of the oldest business models in the book. And all it really boils down to is flat rate service or unlimited support or a flat rate fee, I should say, for unlimited service. My background is in it. Security work for many different i.t. Security companies and government agencies, both foreign and domestic. I worked for. I could tell you it was for some of the really cool ones like the NSA or the CIA. But it’s not. It’s mostly for things like the IRS or the Department of Weights and Measures, which are.
Kameron Kennemer [00:01:58] Very nice. Yes.
DJ Forman [00:02:01] That was an interesting one. We help them develop a triple encryption system for the other agents that were in the field so that their systems had three layers of encryption. Upon encryption. Upon encryption, they don’t do that. Nobody does it that way anymore. But it was fun at the time, so I really appreciate your intro. I’m really looking forward to this as well. I think that this is an opportunity for us to share I.T. knowledge and insights with the rest of the world, who probably is a little confused by reading what they’re reading in the news and the various media outlets. It’s not always very clear. And that’s why that’s what my real goal here is. My real goal here is to be able to explain this stuff, not necessarily in layman’s terms. Right. Sometimes that could be taken a little bit of as a derogatory term more from the perspective of using common business language and, you know, relating i.t. Issues to actual business operations and executive decision-making processes, giving people the information they need to make these difficult decisions at times. And how much do I put in for security? How many layers do I need in my security? Onion How much of the FUD fear, uncertainty, and doubt, how much of that is real? How much of it is just marketing fluff? Sure. That’s one of my biggest goals that you’re trying to accomplish for people. Obviously, you know, we want to learn. We’re a business, we want to generate business. I think it’s more important to share information, share knowledge, and things will happen organically from there. You know, in the art world, I like to think sometimes that there are two different types of people. There’s the type of person who hoards all of their knowledge and experience over the years, and that’s what they believe makes them valuable. They’re not entirely wrong. That is a viable method, right? Secret sauce knowledge, you know, the secret spices and the KFC chicken and what’s know what’s the secret behind the McDonald’s French fries, all that stuff. That’s certainly true. But in my opinion, there’s the other much more rare type of i.t person who I believe is ten times more powerful. And that’s the person, that’s that person who, instead of hoarding that information and knowledge, tries to share it with their peers, tries to share it with the, with clients and everyone around them. That I believe is orders of magnitude more powerful.
Kameron Kennemer [00:04:28] So that is a great philosophy, I think, and it’s one of the things that makes the company strong. As you’ve been still some of those principles in the culture of it. And it really shows. And from what I have seen from our current clients, they really appreciate the type of culture that you’ve created within the company. You’ve obviously got a huge brain, you’re very smart, you’re also a good communicator. How do you fit all of that? How do you fit all of that humbleness and intelligence inside of your skull? That’s what I want to know.
DJ Forman [00:05:05] Oh, buddy. It leaks out every day. I can’t contain it all. I know. Honestly, I just. I’ve been around the block a few times. I like to joke that I’ve got a master’s degree from the School of Hard Knocks. I’ve seen some big failures. I’ve seen some big wins. A good example is when we work with other people, other companies, lawyers, doctors, and various other people with advanced education. These are obviously very smart people. But sometimes, just like when you drive your car, it’s like magic sometimes, right? But what these people, when they use their computers, it’s a bit like magic. They don’t really understand how it all works, in which direction all the bits and bytes are flowing. Nor should they necessarily.
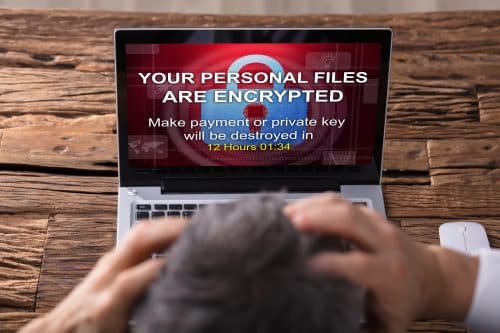
Kameron Kennemer [00:05:48] You know, one of the things that I’m really excited about is the free cybersecurity awareness training classes that we’re going to be doing for business this year. I think that you are going to be a great instructor and a great teacher for those business owners, and then it’s going to be something that really benefits them and helps them to avoid some of the phishing scams and other things that can really leave businesses vulnerable and cost them quite a lot of money. I’m looking forward to helping you put that together, too. Can you talk a little bit about that?
DJ Forman [00:06:19] I’m also looking forward to being able to do more security awareness training for people. I think far too often that kind of training isn’t delivered with the best intentions in mind. But oftentimes when you go to this Cybersecurity awareness training, it’s very focused on all the fun and you’ll hear me say that a lot. “FUD”.
Kameron Kennemer [00:06:41] Fear uncertainty and doubt.
DJ Forman [00:06:42] Right. It’s a classic model. And I don’t remember off the top of my head who coined that one, but it’s used every day in sales and marketing tactics, right? You generate the FUD and then that gets people to want to take action. And the interesting part about that is that’s exactly how the majority of business email compromises and PACs of various types are accomplished. They’re leveraging FUD. It’s one of the biggest things that people need to become aware of whenever there is a call to action. Right. That’s the term that we like to use as a call to action, like, Oh, you better do this, or else that’s a red flag immediately. Anything that says that any communication, any messaging, that’s suspect.
Kameron Kennemer [00:07:33] Right.
DJ Forman [00:07:34] It’s almost always followed up with, here’s the action that we want you to take and it’s login to this service. Change your password. Any number of things that you would think, Oh, wow, there’s a problem. I better move to action. I’ve been called and it’s this thing that’s baked into the human brain a little bit like subliminal advertising is baked into the human brain. And it’s why it’s illegal, because it’s what you’re doing is you’re taking advantage of a mechanism that can’t be controlled. I don’t know if anybody remembers, but back in the day, one of the original methods of doing that is that during movies, they would splice in a couple of frames of a Coke or popcorn, and then they’d have the mid-movie intermission and then the intermission when they played those inserted of those little things that you couldn’t really see, your brain still saw it. And so everybody went out and they like doubled their soda and popcorn sale.
Kameron Kennemer [00:08:29] Reminds me of that scene from Fight Club, which we won’t go into on here. I think everybody is that interesting.
DJ Forman [00:08:37] Interestingly, I literally watched that movie last night while I was trying to fall asleep. It’s very much that it’s very much just like that. It’s a really good analogy. So how do we fight that? Right. And how do we avoid that? Because there is a call to action that does need to happen. But it’s the call to action be educated, be aware, not log in and give me your password. I think at best, by this point we would hope that most people are aware of that, but they’re not. I can tell you that almost on a daily basis we have to retrain people. They’ll get an email that says, Oh, hey, your Microsoft password has been compromised. This is your I.T. administrator. Please log in here and change your password, and it looks proper, looks like it’s something from Microsoft. 365. Hey, they say they’re my I.T. Administrator. I’ve never met my I.T. Administrator. I don’t even know what they look like, so sure. Click type it in boom. Compromised for after that is different in every case, that’s going to be the type of focus that we have is look, we’re going to describe to people here are the things that you should be looking for. Here’s the red flags, here’s the things that you can actually take action on. A lot of times also in these trainings, you’ll see things where they’ll start talking about advanced technologies. Right. But to help the average user, they’re not going to understand any of that. That’s more I.T. Person to I.T. person. So that’s what we try to focus on. We try to make it so that the security awareness training is going to show people, actual people, users, if you will, of the system, what they can actually do.
Kameron Kennemer [00:10:10] Speak is speaking of that, a lot of the i.t cybersecurity awareness training classes that businesses provide for their employees, their recordings a lot of the times aren’t.
DJ Forman [00:10:20] They? Yeah. There’s a lot of prerecorded stuff out there that you can watch and I think that while that has its place, I think it’s more important that it be a live interactive process. That’s one of the best ways to actually learn is you’ve got to interact with people. I can’t tell you how many times I’ve been in a security awareness training program or I’ve been delivering one, and I can watch people, they start to fade away. It’s I mean, how boring is that stuff? Sometimes it’s it can be very boring.
Kameron Kennemer [00:10:49] And for all of you business owners out there who are thinking about getting some cybersecurity awareness training for your staff, I have to tell you that this guy is very entertaining and does magic tricks. He does all kinds of fun things to keep your employees engaged and they will retain the information. It’s interactive. You know, they’re participating in the training versus just watching some prerecorded learning management system where they take a little test at the end of each section. They’re really just looking at their phone the whole time and guessing at the answers until they get them. All right. They didn’t absorb any information 100%. The difference is night and day, this will be effective and it’s free. It’s a win-win because we’re able to network with other businesses out there and provide a valuable service as well. So I encourage you to check it out. We’re going to put a link into the show where you can go and register your staff for the Free Cybersecurity Live Training by D.J. and his team of genius techs from ITEC. And that is going to be fantastic. So other things that I was excited to talk about on this pilot episode, our first episode, we wanted to create a production that is fun, that it’s not just a bunch of nerds sitting around talking about computers and I.T. and networking and cybersecurity and things like that, which we are going to talk a lot about that stuff. That’s the central focus of our show. But we’re also going to be doing fun stuff. We’re going to be having contests with different teams where they’re trying to, you know, hack into systems. And we have other. It seems, trying to stop them. I have a hackathon. We’re going to do live cyber security awareness training. That’s going to be gamified, where we’ll have teams who are able to compete against each other. We want to get some interesting guests on the show, too, maybe some experts from different companies who can talk about their experiences and their perspective. You’re also talking about doing some Mythbusters meets information technology, maybe server meets flamethrower or melting through some hard drives with thermite. We might want to try some of those things out, too. We will see where it goes. What do you think about all that, D.J.?
DJ Forman [00:12:50] It’s like, Yes, yes to all that. I think all that stuff sounds fantastic. We’ve got to keep it entertaining, got to keep people hooked into it so that they want to watch it. They want to watch some geek just drone on and on and on about technical stuff.
Kameron Kennemer [00:13:02] So, D.J., let me ask you about the world of information technology right now. I have previous experience in digital marketing. I’ve worked with a lot of businesses. Not too long ago, there were a lot of brick-and-mortar businesses that didn’t even have a website. But that’s all changing now. Businesses are becoming a part of the Internet of Things, and that creates a lot more vulnerabilities. How do you see that progressing as time moves on? And what can companies do to protect themselves?
DJ Forman [00:13:31] Everybody needs to get a little bit more knowledge. Just like when engineers are tech’s go to seminars and ongoing training and get continuing education credits. Business owners need to do the same thing, and I believe that there’s not system in place for something like that. I believe that business owners are left in this nebulous area of, well, I’m the business owner, so I should already have all the answers or know all this stuff. And I think that that’s a big gap that needs to be addressed. There needs to be an ongoing awareness of things. For example, surveillance cameras. Voice over IP phones, gate entry equipment, door entry equipment, light bulbs, for goodness’ sake. Oh, I’m sorry.
Kameron Kennemer [00:14:22] It’s all connected now.
DJ Forman [00:14:25] Exactly. Everything is connected. And, you know, long ago we talked about this, and years ago we said, oh, someday even light bulbs are going to have IP addresses. Well, guess what? We’re here. Been here for a little while, actually, and it’s not going anywhere anytime soon, other than more literally everything. Your refrigerator, your microwave, your oven, your vacuum cleaner, literally everything is an iota an Internet of Things device that connects to the app on your phone so that you can watch your little Roomba, scoot around the house, and save it. When it gets stuck, it lets you know I’m stuck. Can you run and save it? You’re you know, I’ve got a digital barbecue smoker in my backyard. It tells me exactly when my tricep is ready and when my brisket gets ready, everything is connected. But people need to understand that every single one of those devices is now a computer. Sure, it’s got varying levels of computational power, but it’s a computer. It’s in your network. It’s communicating not just with you and your smartphone app. It’s also connected to the Internet. Keep itself up to date. It’s reaching out to call home, as we like to say. And if you take the time to look at these things, you’ll see the IP cameras they call home quite a bit. Now, you’ve probably heard or if you haven’t, you’re about to hear that there is a list of devices that are not supposed to be used. They’re not allowed to be used in government agencies. There’s a huge range of IP cameras that come from China. Those are on the no-no list. What they have found is that many of those devices call back home and are providing we don’t know what information from the device could be absolutely innocuous potentially, but that’s why, you know, we don’t know. And so that’s why these things are being blocked. That said, what if you have, you know, forget the international politics and government angle, We definitely don’t want to go down that rabbit hole. But what if you’ve got a device that is legitimately calling home to its manufacturer for patches, updates, and things like that? So doing the normal things that need to do well, there is a specific brand that we aren’t going to name at the moment that has a compromise of that back-end system. And what ended up happening is that these IP-based video surveillance cameras were wide open to the world so that someone can get into that camera, put a little bit of software on there to do anything that we wanted, that they want it to do, scan the network for other devices, try to access other devices, listen to the traffic on the network, try to collect sensitive information, personally identifiable information. And at first glance, a lot of companies will say, well, we’re just an electronic electrician company, we’re just a bunch of plumbers. Well, I got news for you. You’re the number one target. And any time you find yourself saying, Well, we’re just a flower company, or whatever the case may be, please realize you’re the main target. Not because they necessarily are trying to steal your information, though that is part of it, but they’re trying to use your network as a jumping point for various other types of nefarious activity. So people have to start thinking a little bit more outside the box in terms of, well, we’re just an X, Y, Z company, we’re not a target, we don’t have anything valuable. We’ll probably have more valuable, more value than you think that you do. Now, a lot of people will say, okay, well, if that happens, then we just shut down the network and you know, then we fix the problem, we move on. Well, that’s not what happens. You’re not liable if an attack comes from your network. You’re you have some major legal problems to potentially get around. You’ve got privacy violations based on what state you’re in. You’ve got various other compliance issues. The big ones, the people, as most people know, are HIPAA for health care, Right? I or II, which is personal health information or electronic personal health information, There’s the PCI, DSS compliance standard for anybody who has credit cards, your retail space, and you swipe your credit cards, or even if you go into a web portal and type in credit cards, if you’re an online retailer with, you know, Etsy or whatever else you need to be compliant. And if you’re not, there’s a huge legal issue involved and massive fines. What’s going to end up happening in those compromises that people don’t understand is that if you’re compromised and the auditors are going to come in, they’re going to check all your systems and there’s a penalty in punishment for every single record, and every single credit card that’s been compromised, whether any damage has been done or not, you’ve already broken the law. And that’s the real problem. When. When you hear those super scary statistics, like 80% of all businesses that experience a compromise are out of business within a year or two. That’s what they’re talking about. That’s a.
[00:19:33] Little bit of that’s a little bit of hyperbole, but it’s not inaccurate.
Kameron Kennemer [00:19:38] So we do spend a lot of time talking about cybersecurity and some of the consequences that can happen. Can you talk about some of the benefits that companies can receive by a company like it?
DJ Forman [00:19:51] Yes. It’s not all doom and gloom. There’s a lot to be gained from this and specifically about I.T. security, but about all I.T. technology. When you deploy these things, it offers you operational management opportunities to help streamline that side of your business and to help you do things, for example, account access when you’re deploying, let’s say, multifactor authentication, when you’re deploying a managed version of it. Now, we’re not talking about like when you log into your Google and it sends your phone a text number. That’s okay. That has to factor. But as you have read in the news just this week, Google has pushed forward with a passwordless system. We’ll talk about that more later because there’s a lot to understand about that. When you do have centralized management technology tools, some security-based ones, but also just regular operational things. You gain a measure of control so that you can know the who, what, where, and why of things, who accessed what information, when they accessed it, where they accessed it, and where did that data go and why? Why was this done this way? You get all of those the big five W’s of journalism, right? Like of who, what, where, and why. You get all of that information from these tools so that you can have an understanding. Now, I don’t want to step on anybody’s management style, but in my opinion, in my experience, oftentimes metrics like these can be maybe misused a little bit used a little bit heavy-handedly to make some assumptions about people and make hiring and firing decisions and all that good stuff, or to make it an evaluation of. How hard somebody is working or how much they’re working. Yes, you can absolutely use those tools for those things. I don’t agree that all of it is accurate. I think there’s a lot that can be assumed by that and assumed incorrectly. However, there are also some very powerful tools in there to help guide your process along so that you can know the who, what, where, and why of things and then make a determination moving forward. Most people’s networks now and their technology deployments, they don’t have that. They hope that that’s how it works, but they don’t know it. They don’t have any way to measure that. So they have to guess.
Kameron Kennemer [00:22:18] I think that one of the biggest things that made me excited to come to work with it is your philosophy of how to deal with people being real with people and being genuine with people and not trying to scare them to death into doing business with you. And I think that when you are coming from a genuine interest in helping a company and being somebody who isn’t just trying to make a sale to them but to actually forge a partnership where moving forward you guys can rely on each other. It’s a win-win dynamic where they’re helping you and you’re helping them. I really like that. And I think, you know, a lot of companies out there, they lose focus on what’s most important. And I know you and I have had a lot of conversations about this in the past about how important it is, how you treat your customers, and how that affects the development of your business moving forward. And really the trends in business have kind of this downward spiral where they’re expecting more and more out of their employees all the time and they always feel rushed to get things done. And now that’s compromising the service that you give to people, which has a negative effect on your company. So you’re making less revenue and then you’re pushing people even harder because of this culture, this dirty culture that you’ve set up in your company. Yeah, that’s something that often I’ve thought, Man, when is this going to win? Are companies going to going to get it together and start really focusing on what’s in the best interest of their clients? And I think we’re doing a pretty good job with that. We can always do better, but I think that’s something we’re doing a good job with.
DJ Forman [00:23:47] Without a doubt. Nobody’s perfect, certainly not myself. So many flaws. You know, I, I try to follow the saying, you know, know thyself. And that’s difficult because that requires you to look in the mirror a lot. And that can be a challenge. But aside from that philosophy, there’s also the hard-core philosophy of paying yourself first. It’s a very common theme in business networking groups. It’s a very common thing in business, but from business coaches, and a lot of the most famous people who are out there and doing their own video blogs, Gary Vader checking comes to mind as a big one that I’ve listened to some of their stuff or his stuff. And, you know, there’s a very common theme of paying yourself first. I can’t tell you that that’s wrong is a lot of people make a lot of money operating their businesses that way. There’s room for all different types. What I believe is important and that’s how I try to operate. No marketing person I’ve ever worked with wants me to say this out loud, but I’m going to say it right now. We give a shit. We care about your people. We care about your company. Now, before anybody starts thinking, Oh, wow, this, that, they’re all super altruistic and we’re not all that, it’s if there’s a little bit of a self-serving element to that. If we don’t care, then how like, your success directly determines our success as a provider of I.T. support and securities management services. So it’s kind of a matter of you have to I can give you.
Kameron Kennemer [00:25:20] This advertisement is word of mouth advertisement, and it makes a big difference. When I was younger, my first job out of high school, I was a busser. I worked in a restaurant, in a hotel. The name of the company was Red Lion Hotel Corporation. It was a great company and they instilled in me, All you have to do is focus on the customer, focus on their needs and fulfilling their needs, and anticipate their needs before they even know that they have them. And that’s what good services are. And as long as you’re focused on that, as long as you are making sure that that is your purpose, then you’re going to be successful in all of the other metrics. You’re going to build a name for yourself. People are going to talk to their friends and say, Wow, I had this great experience with this company. And that kind of reputation building takes a long time because people are much more likely to talk about a bad experience that they’ve had with a company versus a good experience for every one time they talk about a good experience they had in a company, they’ll tell ten stories about a bad experience that they had at a company. So really important to focus on that. And, you know, I’ve just seen the culture change a lot. Unfortunately, in corporate America, money is first, and maybe the customer is second. You know, if. If you’re lucky. The bottom line is the dollar. And I think that’s really the wrong focus. What is most important? Remember what you got into business for. Hopefully, it wasn’t just to make money. Hopefully, it was to provide some valuable service to people out there.
DJ Forman [00:26:54] We could probably debate that kind of stuff all day long.
Kameron Kennemer [00:26:57] You’ve got great experience as a business owner. This isn’t the first business you’ve started, is it? Can you tell our listeners about some of the other businesses you’ve had? I think they’re very interesting and people would like to hear about them.
DJ Forman [00:27:10] One of the most successful ones that I did was installing televisions, and entertainment systems in hospitals. So we not only sold them their TVs but installed them in patient rooms, operating rooms, all the different facilities hooked up multiple satellite feeds off air antenna dishes, cable providers, consolidate all these things so that when you’re in the hospital, you get your 500 channels of various content. But it’s not tied to that. It’s actually very similar to what we did in hotels as well. It’s very similar to what happens in those environments. You go in there and you’re looking through the scroll, you’re at the list of all the channels and you’re like, What? What is this? I’ve never seen anything like this. It’s because that’s what they’re doing. They’re pulling in all these different feeds of information. They’re consolidating it down and they’re making their own channel up. Nowadays can be a little bit different with the ubiquity of various services. There are some places that will say, Well, we have dish TV or well, we’ve got, you know, cable service and whatever channel lineups they provide. So the industry has changed. But that was something that we did for many years.
Kameron Kennemer [00:28:22] And did you use the BlackBerry ringtones, too? Yeah.
DJ Forman [00:28:28] So in my garage at my house back in the early days, I had several racks of servers. Which one of these days will show you on the show is now turned into my son’s young man cave, where they do their computer gaming and whatever Twitch streaming and whatever stuff that they like to do. But that used to be a room filled with racks of servers so that all the ringtones that people used to buy for their Blackberries and, you know, little snippets of songs from popular artists and things like that, we hosted them here all over the world. This is where you got it from. You just never knew it was cool. BlackBerry imploded, of course. I know they still exist as a company, but I don’t know.
Kameron Kennemer [00:29:07] My wife used to love those. She had a little pink one with the trackball on it and she thought that was the coolest thing in the world.
DJ Forman [00:29:13] I had so many Blackberries. I actually have fondness and sadness in my heart because I thought they were fantastic devices. I loved mine.
Kameron Kennemer [00:29:23] She did too. She really liked them. But. Oh well, move on. Do you’ve had a lot of great experience as a business, as a business owner, and you’ve, you know, given some really great advice to our listeners out there? Could you also give some advice to people who are maybe looking to get into or switch careers in information technology? Could you give them some advice on maybe how to go about that?
DJ Forman [00:29:47] Don’t do it. It’s just like any service tree service industry. It can be a little stressful. But I have found that the best I.T. people weren’t born I.T. people. They had another life doing something else. I have found that those that are more inclined to be musical tend to be very, very good in I.T., I have found that those with ADHD and things of that nature, they tend to do really well, and I do. But when you’re crossing disciplines over, it’s it doesn’t have to be as difficult as you might think. You don’t have to have one. Like I’ve been in this business for a long time, I mean, since pre-Internet was on several different teams of, of testing Internet before it wasn’t available to the public. So I’ve seen it evolve from the inside all the way to where it is now. And I can tell you, you don’t have to have that. Certainly, you have to have that to be somebody like me. But to get into the business, you don’t need that. You can gain so much. You do have to find the right team, Right? The right team. Like I sometimes will talk about the two different types of i.t people, the ones that keep their knowledge siloed and private, and that’s their value. And those that share that information with everyone around them, their peers and their teammates, and people exponentially more powerful than the person who shares. But by quantity, more people silo. So what you want to do is you want to find the right team. Certainly get a little education, build your own computer, things like that. You know, get used to some of the ins and outs of some of the basic stuff, but then you’ve got to find a team that is in the open silo that’s going to share information, that’s going to actually mentor you and tell you things because that can be the biggest challenge in this industry, is a lot of people will say, well, I’m going to go get some training in college, not going to go get an I.T. job somewhere. And then they’re very upset because they find themselves sitting on a help desk in a. A room with 200 other people taking, you know, level what we would call a level one phone call about basic issues. And they get kind of stuck there. They’ll be reading scripts off of screens. And that’s not well, that’s part of it. That’s a different kind of it. And so you have to really understand where you want to be. You’re going to be in that world. There’s nothing wrong with that. It’s absolutely required. And some of my favorite and our the best people in our team just do that all day long. That’s hard. That’s challenging. I have nothing but the utmost respect for them and empathy because they have to deal with a lot of stress that’s coming at them and being able to put that wall up, filter it and listen with their ears instead of their mouth, but really filter. What is this person saying? Somebody is calling up and saying, Oh, I the Internet’s down. Like, well, pretty sure it’s not because on my third screen, I’ve got a YouTube video playing right now and producers, man. But what does that mean to them? That’s an easy one because it’s obvious, right? The Internet’s not working for them. But when people are heated and they’re upset, they’re going to say things and they’re going to say things that really can confuse the matter. And so having the ability to logically disassemble what somebody says versus what they actually mean is probably one of the most important parts of being in it, to be able to understand how to filter that, how to convert it. But then I got to tell you, you’ve got to be a therapist. You have to be good with people. You have to be willing to listen to people. If you don’t if you’re one of those types that doesn’t like people, like a super extra introvert, or maybe you’re even like, know thyself, right? You know that you’re a little curmudgeonly, it’s heartless. You don’t really people, you are like”People suck!”. Maybe I.T. is not for you because you’re going to have to deal with people every day. So I would say that the biggest tip is, to find someplace that shares information with you but has an open silo type of place. But to have a little bit of psychology in here, maybe in school, take a semester of Psych 101 to understand kind of the basics personally, my first vocation was law enforcement. It’s called the Administration of Justice. AJ Is that as we said or as we say in college and stuff? So I veered heavily out of that direction. But I can tell you that the skills that I learned there get applied to what I do here every day. So that’s the biggest advice I have for you, is that don’t think that if you’re geeky and nerdy that that’s the end all, be all. Don’t think that if you’re not geeky and nerdy that prevents you from getting in, It absolutely does not. So please join us. We need you.
Kameron Kennemer [00:34:15] D.J., you are a wealth of information. I look forward to learning from you. I’m super excited about working with you in the future, working with our show, and bringing valuable content to our viewers. Folks, thanks for listening to ITcurio. Be sure to subscribe to our show on your favorite platform and follow us on social media for more episodes in the future. And don’t forget to sign up for our free cybersecurity awareness training class, and you can go there by following the link at the bottom of the screen here. Thank you so much. Until next time. Have a great day!

Pingback: The IT Curio Show: Blog Episode 1 – Introducing ITque and Exploring the Intersection of Technology and Business – The ITcurio Podcast